Want to know more about this keyless cash transit solution?
TransitoLocker offers bank offices an easy and secure way to open safes or lockers, without the use of cumbersome key chains. Moreover, all events are carefully logged in the system to ensure a clear oversight.
Key management made easy
Key management is complex. Easy versions are insecure and secure versions aren’t easy to use. Conventional keys are relatively easily lost or stolen. Besides, there is the risk of a robbery, because the lockers can be opened without delay.
The TransitoLocker concept works with standard MiFare key cards, often already in place in secure environments, for access management purposes. Once a user is authorised, he can open the lockers with his own key card.
TransitoLocker powers up to 16 lockers, which can only be opened one-at-a-time.

What makes TransitoLocker unique?
How does TransitoLocker work?
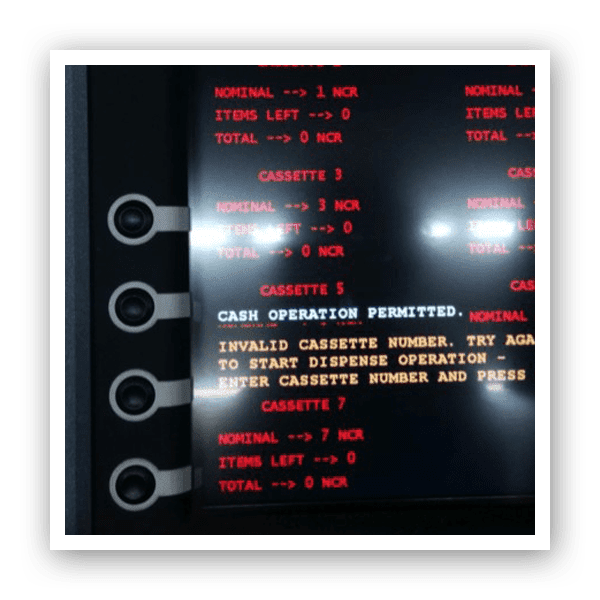
The user presents his MiFare key card to the TransitoLocker and enters his PIN. Subsequently, he chooses the locker that needs to be opened, which will activate the time lock delay sequence. The delay is programmable to fit the needs of your environment (standard set to 4 minutes). When the timer has expired, the user presents his card again, re-enters his PIN and the correct locker will be opened.
Features & benefits
- Easy to use
- Works with standard MiFare access management key cards
- Secure; time lock delays opening
- No more lost or stolen keys
- Easily add, edit or remove users from the system
- Event logging; see who opens which locker at what time
- Optional: remote opening from control room

Beat ATM & CIT crime at the source
Cash money is very appealing to criminals; always has been, always will be as long as there is cash money in circulation. Over the years, there have been quite some changes in the types of attack. In many (European) countries, bank robberies occur less and less, because there is hardly any cash on site. The ATM has taken over this role and has subsequently become a target. The CIT business is also a target for extremely violent robberies. To break the arms race between criminals and the cash handling industry, we believe we need to address the problem at the source: remove the reward to remove the crime.

Attacks on ATMs
Explosive attacks on ATMs happen on a daily basis in many countries. Criminals use trucks and excavators to ram the ATM out of the wall and explosive gas (often a mixture of acetylene and oxygen) or solid explosives, like hand grenades and plastic explosives, to access the cash cassettes in the ATM. If necessary, the door to the vault area is rammed with a ‘battering ram’ attached to a car. Since a couple of years, off premise ATMs in supermarket have also become a target for criminals. The damage involved in these attacks is enormous. So it makes perfect sense that banks show an interest in solutions like the GPU (Gas Protection Unit) and GlueFusion (cash degradation with glue, inside cash cassettes).

Attacks on CIT
Cash handling has many aspects; from delivery of the cash, servicing ATMs and transporting cash, to counting and sorting in the cash centers. Every aspect has its own risk moments, positions and MO’s (Modi Operandi). During attacks on the Cash in Transit operation, criminals are using increasingly heavier and more dangerous weaponry. Automatic firearms and plastic explosives are used to shoot at and blow up armored trucks. The CIT custodian is also frequently a target of an attack. In the Netherlands, attacks on the custodians are very rare these days. Main reason for the decline of this MO is the use of the MactwinBox, with irreversible cash degradation.
The future of attacks on the Cash Handling industry
By using irreversible cash degradation – also known as IBNS (Intelligent Banknote Neutralisation Systems) – on a large scale in ATMs and CIT operations, the number of physical attacks will decrease drastically and criminals will be forced to explore other targets. We don’t really expect them to get honest jobs (wishful thinking), but believe their focus will shift further towards cybercrime (e.g. jackpotting). In the next couple of years, organizations will need to invest substantially in improving their digital defensibility.
We are proud to work for these organizations
Over the past 30 years we have helped numerous banks and CIT-companies improve their security. We implemented large-scale camera surveillance, designed complete cash centers and helped develop specific cash solutions. We proudly call these companies our partners:
Contact Us Today
Interested in a demonstration or more information?
Please, send us your details and we’ll gladly contact you soon!
Click here for our Privacy Statement.